By Dale Vile
If you are feeling inadequate because you’re not in full control of your virtual server environment, give yourself a break. In a recent research study conducted by Freeform Dynamics, many of the 400 plus participants told us about challenges that are causing significant problems or unwanted distractions in this area.
This didn’t surprise us because we run into people all the time who are experiencing virtual server sprawl – a phenomenon that received a lot of attention a few years ago, but isn’t talked about much today. The research confirms, however, that the problem is still very much with us.
For those not familiar with the concept, it’s not hard to understand. When IT teams get used to how easy, convenient and quick it is to create new virtual machines (VMs), they end up generating lots of them. The trouble is that people are not very good at keeping track of what’s been created, or disposing of VMs when they are no longer needed. This is a particular problem if you use virtual servers for transient requirements in areas such as development, testing and support. Issues can also arise in other situations when VMs lie dormant for long periods, as often happens in disaster recover (DR) setups, for example.
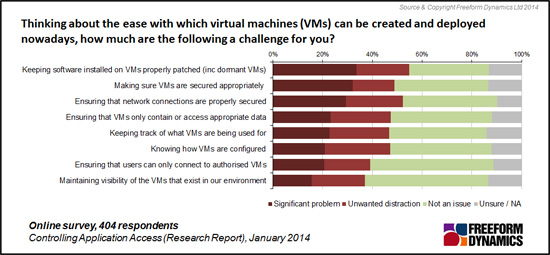
Many of the challenges reported are to do with familiar administration tasks – asset and configuration management, software patching, and generally keeping track of the VMs that exists and what they are being used for (Figure 1).
Figure 1
Charts like this can be informative, but they can also be deceptive. Despite the amount the green (‘Not an issue’) responses, the underlying data tells us that around three quarters of those participating the study have challenges (just in different combinations), with larger organisations running broader server estates not surprisingly suffering the most.
More apparent from this chart is that the problems don’t just translate to administration overhead. Difficulties making sure VMs are properly secured, including with respect to who has access to them and any sensitive data they contain, are also highlighted. Something often overlooked is then the need to ensure that network connections used by VMs are properly secured. This is a particular concern as virtual servers increasingly underpin core business systems and externally facing web applications.
From a solution perspective, technology exists to help deal with all of the challenges highlighted in the research. This ranges from tools to assist with the management of virtual server landscapes themselves, to application-aware appliances that monitor and enforce security at the network level to act as a safety net.
Against this background, while we would not discourage anyone from looking at more advanced virtualisation approaches that many vendors are now promoting under the ’software defined everything’ theme, we would urge you not to forget some of the basics we have been discussing to do with your existing virtual server environment.
If you are interested in reading more about the context for this discussion, we would encourage you to download the full study report entitled “Controlling Application Access”, which is available free of charge and without registration here.

Dale is a co-founder of Freeform Dynamics, and today runs the company. As part of this, he oversees the organisation’s industry coverage and research agenda, which tracks technology trends and developments, along with IT-related buying behaviour among mainstream enterprises, SMBs and public sector organisations.





Have You Read This?
From Barcode Scanning to Smart Data Capture
Beyond the Barcode: Smart Data Capture
The Evolving Role of Converged Infrastructure in Modern IT
Evaluating the Potential of Hyper-Converged Storage
Kubernetes as an enterprise multi-cloud enabler
A CX perspective on the Contact Centre
Automation of SAP Master Data Management
Tackling the software skills crunch